dnsReaper - dnsReaper - 攻击者、漏洞赏金猎人和蓝队的
Created at: 2022-07-19 16:17:30
Language: Python
License: AGPL-3.0
DNS Reaper
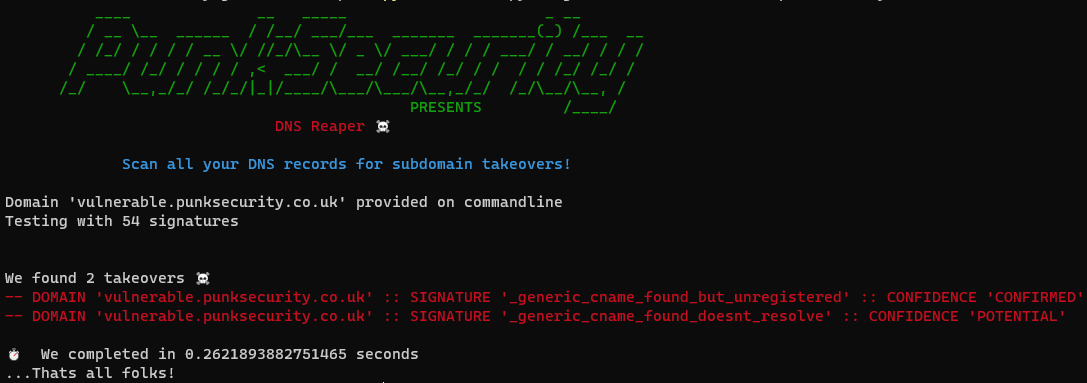
DNS Reaper是另一个子域接管工具,但重点是准确性,速度和我们武器库中的签名数量!
我们可以每秒扫描大约50个子域,用50多个接管签名测试每个子域。这意味着大多数组织可以在不到10秒的时间内扫描其整个DNS资产。
你可以使用DNS收割者作为攻击者或错误猎人!
你可以通过在文件中提供域列表或在命令行上提供单个域来运行它。然后,DNS收割者将扫描域及其所有签名,生成CSV文件。
你可以使用DNS收割者作为防御者!
你可以通过让它为你获取你的DNS记录来运行它!是的,没错,你可以使用凭据运行它,并快速轻松地测试所有域配置。DNS收割者将连接到DNS提供商并获取所有记录,然后对其进行测试。
我们目前支持 AWS Route53、Cloudflare 和 Azure。可在此处找到有关添加自己的提供程序的文档
你可以使用DNS Reaper作为DevSecOps Pro!
Punk Security是一家DevSecOps公司,DNS Reaper植根于现代安全最佳实践。
你可以在管道中运行 DNS Reaper,向其提供要预配的域的列表,如果它检测到可以进行接管,它将退出 Non-Zero。你可以在收购成为可能之前就阻止他们!
用法
要运行 DNS Reaper,你可以使用 docker 映像或使用 python 3.10 运行它。
结果在输出中返回,并在本地“结果.csv”文件中提供更多详细信息。我们还支持 json 输出作为选项。
使用泊坞窗运行它
docker run punksecurity/dnsreaper --help
用python运行它
pip install -r requirements.txt python main.py --help
常用命令
-
扫描 AWS 账户:
docker run punksecurity/dnsreaper aws --aws-access-key-id <key> --aws-access-key-secret <secret>
有关更多信息,请参阅 aws 提供商的文档
-
扫描文件中的所有域:
docker run -v $(pwd):/etc/dnsreaper punksecurity/dnsreaper file --filename /etc/dnsreaper/<filename>
-
扫描单个域
docker run punksecurity/dnsreaper single --domain <domain>
-
扫描单个域并输出到标准输出:
你应该重定向 stderr 输出,或者使用 > 保存 stdout 输出
docker run punksecurity/dnsreaper single --domain <domain> --out stdout --out-format=json > output
完全使用
____ __ _____ _ __
/ __ \__ ______ / /__/ ___/___ _______ _______(_) /___ __
/ /_/ / / / / __ \/ //_/\__ \/ _ \/ ___/ / / / ___/ / __/ / / /
/ ____/ /_/ / / / / ,< ___/ / __/ /__/ /_/ / / / / /_/ /_/ /
/_/ \__,_/_/ /_/_/|_|/____/\___/\___/\__,_/_/ /_/\__/\__, /
PRESENTS /____/
DNS Reaper ☠️
Scan all your DNS records for subdomain takeovers!
usage:
main.py provider [options]
output:
findings output to screen and (by default) results.csv
help:
main.py --help
providers:
> aws - Scan multiple domains by fetching them from AWS Route53
> azure - Scan multiple domains by fetching them from Azure DNS services
> bind - Read domains from a dns BIND zone file, or path to multiple
> cloudflare - Scan multiple domains by fetching them from Cloudflare
> file - Read domains from a file, one per line
> single - Scan a single domain by providing a domain on the commandline
positional arguments:
{aws,azure,bind,cloudflare,file,single}
options:
-h, --help Show this help message and exit
--out OUT Output file (default: results) - use 'stdout' to stream out
--out-format {csv,json}
--parallelism PARALLELISM
Number of domains to test in parallel - too high and you may see odd DNS results (default: 30)
--disable-probable Do not check for probable conditions
--enable-unlikely Check for more conditions, but with a high false positive rate
--signature SIGNATURE
Only scan with this signature (multiple accepted)
--exclude-signature EXCLUDE_SIGNATURE
Do not scan with this signature (multiple accepted)
--pipeline Exit Non-Zero on detection (used to fail a pipeline)
-v, --verbose -v for verbose, -vv for extra verbose
--nocolour Turns off coloured text
aws:
Scan multiple domains by fetching them from AWS Route53
--aws-access-key-id AWS_ACCESS_KEY_ID
Optional
--aws-access-key-secret AWS_ACCESS_KEY_SECRET
Optional
azure:
Scan multiple domains by fetching them from Azure DNS services
--az-subscription-id AZ_SUBSCRIPTION_ID
Required
--az-tenant-id AZ_TENANT_ID
Required
--az-client-id AZ_CLIENT_ID
Required
--az-client-secret AZ_CLIENT_SECRET
Required
bind:
Read domains from a dns BIND zone file, or path to multiple
--bind-zone-file BIND_ZONE_FILE
Required
cloudflare:
Scan multiple domains by fetching them from Cloudflare
--cloudflare-token CLOUDFLARE_TOKEN
Required
file:
Read domains from a file, one per line
--filename FILENAME Required
single:
Scan a single domain by providing a domain on the commandline
--domain DOMAIN Required